28% of Public-Facing Domains Have No DMARC
Q1 2026 scanner data shows 28% of public-facing internet domains have no DMARC record at all. The gap, the consequences, and the two-DNS-record fix.
DMARC is a small piece of DNS that tells the world's mail servers what to do when someone sends a message claiming to be from your domain. Without it, anyone can send email pretending to be you, and there's nothing your domain can do to stop them. We analyzed data from thousands of public-facing internet domains and found that 28% have no DMARC record at all. If you own a domain and have never set up DMARC, there's roughly a 1-in-4 chance you're in this group.
This article unpacks the engaged-vs-internet comparison from DMARCeye's Q1 2026 industry report. The full report, with all 12 chart views and methodology, is below.
The Adoption Gap
The Q1 report compares two populations. The first is the DMARC-engaged group: domains under active monitoring on the DMARCeye platform. The second is a broad public-scanner sample of public-facing internet domains, scanned blindly for DMARC, SPF, and DKIM record presence.
The headline difference, in plain numbers:
- Public-facing internet (scanner sample): 28% have no DMARC record, 32% are at
p=none, 22% atp=quarantine, 18% atp=reject. - DMARC-engaged organizations: 0% have no DMARC by definition, 36.7% at
p=none, 36.8% atp=quarantine, 26.5% atp=reject.
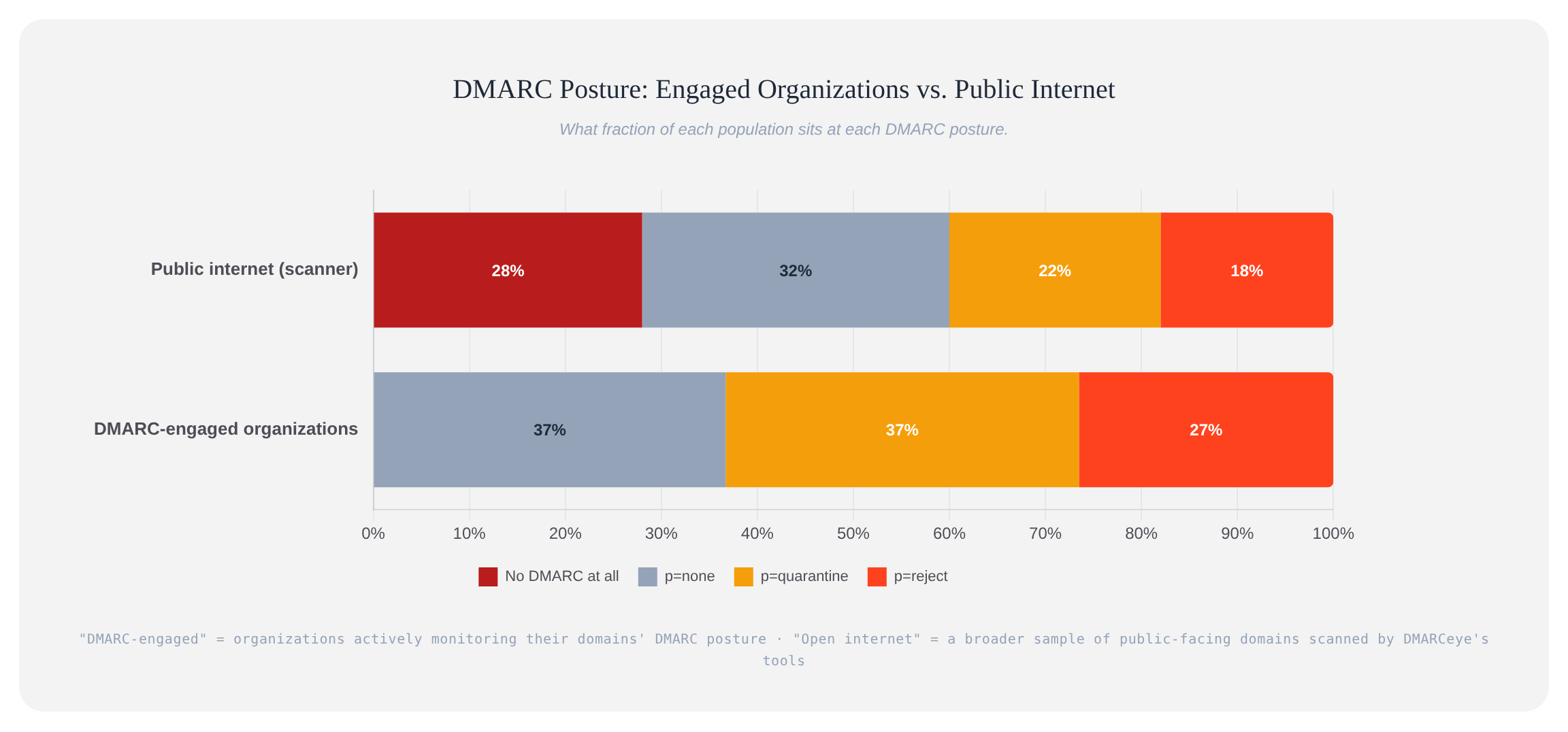
Stricter enforcement is more common in the engaged group: 27% at p=reject versus 18% in the wild. The more telling difference sits at the other end. Once a domain owner takes DMARC seriously enough to monitor it, the "no record published" tier disappears. Out in the wild, that tier is more than a quarter of all domains.
What "No DMARC" Actually Means
Without a DMARC record, your domain stays silent. When a message arrives claiming to be from you, the receiving mail server (Gmail, Yahoo, Seznam, anyone) has no instruction from your side about how to handle it. It falls back to its own filtering. Some spoofed messages get through, some land in spam, some get refused. The result varies, and you have no visibility either way.
For the domain owner, the practical situation is:
- Anyone can send mail in your name with no enforcement against them. A spoofed message will be evaluated by the receiver as if it might be legitimate, because no policy says otherwise.
- You get no feedback. No DMARC record means no aggregate reports flow in. You don't know who is sending mail as your domain, legitimate or otherwise.
- You aren't compliant with bulk-sender requirements. Google and Yahoo's February 2024 sender rules require a DMARC record published for senders above 5,000 messages per day to Gmail or Yahoo addresses. No record means no compliance, full stop.
The fix for "no DMARC" is shorter than the fix for "stuck at p=none." It is two DNS records and a few hours of attention.
Why So Many Domains Have Nothing Published
The Q1 data shows the size of the gap, not its causes. The reasons below are patterns we see across customers, not findings from the dataset:
- The domain owner has never heard of DMARC. The standard exists, the tooling is mature, but the domain owner is a small business or a hobbyist who has never been prompted to publish anything.
- The domain doesn't send much mail, so DMARC never came up. Personal domains, side-project domains, dormant business domains. The volume is low enough that the owner has never run into a deliverability or spoofing problem yet.
- The domain was set up before DMARC was common practice. A domain registered in 2008, configured for email at the time, never revisited.
- The hosting or email provider didn't push the customer to set it up. Some providers walk customers through SPF and DKIM but stop short of DMARC. The customer assumes they're done.
What This Means If You're in The 28%
If you run a small business, an e-shop, a freelance consultancy, or a side project, and you've never thought about DMARC, there's roughly a 1 in 4 chance you're in the no-record-published group. The consequences of staying there:
Your domain is a free target for spoofing. No published policy, no enforcement. Whatever the receiving server's default is, applies. For a domain that doesn't send much mail, the spoofers can fly under the radar for a long time.
You have no visibility into what's being sent as you. Without aggregate reports, the first time you find out about a phishing campaign in your name is usually when a customer or partner asks you about it.
If you ever scale up your sending, you'll have to set DMARC up under pressure. When your monthly volume crosses Google's 5,000-per-day threshold, the bulk-sender requirements kick in and you have to add a DMARC record at the same time you're trying to actually scale your business. Better to do it before that point, when there's no pressure.
The Fix Is Short
Going from "no DMARC" to "monitor-only with reports flowing" is the easiest milestone in this whole space. Three to four steps, an afternoon of attention, no budget required.
Step 1: Check your domain. Type your domain below to see what's currently published. If there's no DMARC line in the result, you've confirmed where you stand.
Step 2: Publish a DMARC record at p=none with reporting. The minimum useful record is one line in your DNS: v=DMARC1; p=none; rua=mailto:reports@yourdomain.com, where the rua address is one you control or one your monitoring service provides. This says: "I'm starting to watch."
Step 3: Get reports flowing in. DMARCeye's free plan covers one domain. It collects the aggregate reports, parses them, and shows you what's actually being sent in your name. Two to four weeks of data is usually enough to see the picture.
Step 4: Tighten the policy as you confirm legitimate senders. Once you can see what's being sent as your domain, authenticate the legitimate senders, then move toward p=quarantine and eventually p=reject. The point of DMARC is to reach actual enforcement, not to publish a record and stop.
The Practical Takeaway
The 28% of domains with no DMARC at all is not a story about technical complexity. The standard has been around since 2015. The records are two short lines in DNS. Free tooling exists for monitoring, including from DMARCeye. The reasons most of these domains have nothing published are not technical. They're at the level of awareness, ownership, and prompting.
If you've made it this far in an article about DMARC, you've taken yourself out of this group simply by reading. The next step is publishing the record.