1 in 3 Small Domains Can't Authenticate Email
Q1 2026 data: 35.7% of domains sending under 100 emails a month authenticate below 50%. Why small senders fail at DMARC and how to fix it in an afternoon.
Among the thousands of domains DMARCeye actively monitors, the smallest senders, those sending under 100 emails a month, average 62.3% DMARC compliance. The largest senders, those sending over 10 million a month, average 99.8%. That gap is striking on its own. The more uncomfortable finding sits underneath the average: 35.7% of those small-volume domains authenticate below 50%. From a DMARC standpoint, more than a third of them are effectively broken.
This article unpacks the small-sender finding from DMARCeye's Q1 2026 industry report. The full report, with all 12 chart views and methodology, is below.
The Size Paradox in DMARC Compliance
Q1 2026 data from DMARCeye's monitoring platform shows a clean staircase pattern. Average compliance climbs with monthly email volume:
- Under 100 emails/month: 62.3%
- 100 to 1,000: 85.7%
- 1,000 to 10,000: 89.9%
- 10,000 to 100,000: 91.7%
- 100,000 to 1 million: 93.9%
- 1 million to 10 million: 97.5%
- Over 10 million: 99.8%

The averages hide the spread. Within each volume tier, the share of domains running below 50% compliance, the "broken" tier in the report, drops sharply as volume grows.
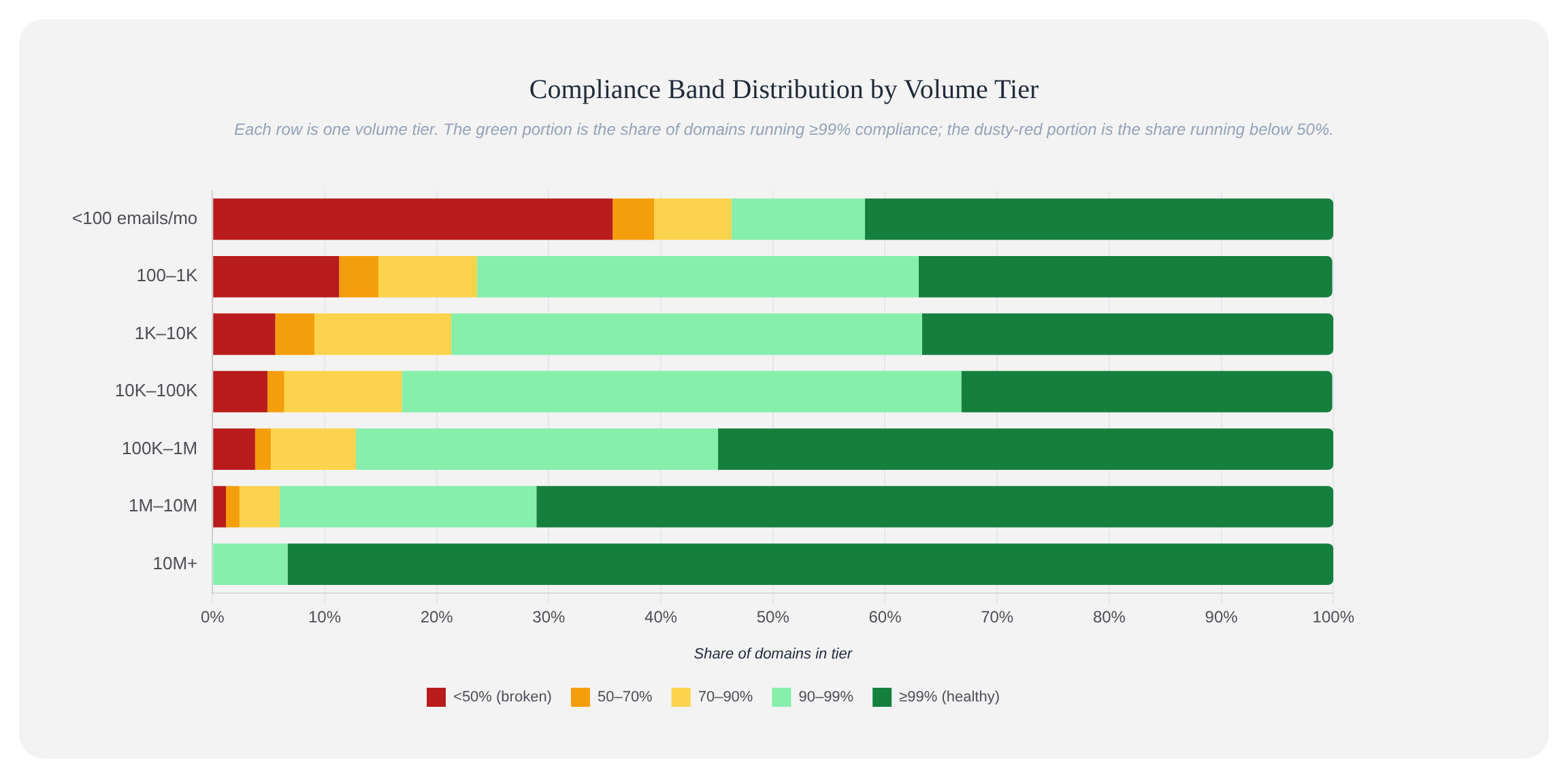
- Under 100 emails/month: 35.7% sit below 50% compliance.
- 100 to 1,000: 11.3%.
- 1,000 to 10,000: 5.6%.
- Over 10 million: 0%. No domain in this tier falls below 90%.
So the headline is not "small senders are slightly behind." The headline is that roughly one in three small senders, domains that send under 100 emails a month, has a DMARC posture that fails most of the time when checked.
Why Small Senders Struggle
The Q1 data shows the pattern, not the cause. The reasons below are patterns we see across customers, not findings from the dataset. Treat them as starting points to check against your own setup:
- SPF and DKIM were never set up correctly to begin with. Many small domains publish a DMARC record, but the underlying SPF and DKIM alignment was never wired through any of the services that send mail as the domain. With nothing aligning, DMARC has nothing to authenticate.
- One forgotten sender drags the percentage down. A small domain that sends 80 legitimate messages a month and one weekly invoice from a misconfigured accounting tool has a 12% authentication failure rate from a single source. At low volume, single bad senders dominate the percentage.
- No one is reading reports. DMARC aggregate reports show the problem. Small businesses rarely have anyone monitoring them. The same misconfiguration that broke things three months ago is still breaking things today.
- DMARC records published without follow-through. Some domains publish a DMARC record because a hosting provider or a how-to article said to. The record is correct, but nothing else is set up to back it up.
The point of monitoring is to find out which of these apply to your domain.
What This Means If You Run a Small Business
If you send a few dozen emails a month from your domain (order confirmations, invoices, the occasional newsletter, password resets, replies to customer inquiries) and you have a DMARC record published, there's roughly a 1 in 3 chance your authentication is broken right now. The consequences:
Your real mail lands in spam more often than it should. Receiving servers like Gmail, Yahoo, and regional providers track failed-authentication patterns against your domain. A broken authentication setup degrades your sender reputation, which gets factored into delivery decisions. Order confirmations and invoices that should arrive within minutes start arriving in spam folders or arriving late.
Spoofers can pretend to be you with no cost to them. A DMARC record at p=none with broken authentication does not stop spoofing. The failed authentication of a real spoofing attempt looks identical to your own broken legitimate mail. The receiving server has no way to tell the difference.
The fix is usually small. One misconfigured sender, one missing SPF include, one DKIM key never published in DNS. Small domains have small surface area. The investigation is correspondingly short.
The Fix
If your domain is in the under-100-emails-a-month tier and you want to check whether you are in the 35.7% broken group, the path is short:
Step 1: Run a free DNS check using DMARCeye's DNS checker. Type your domain below. If you have no DMARC record at all, that's its own problem (and you're in good company; most small domains don't). If you have a DMARC record but no clear SPF or DKIM, you have probably found the problem already.
Step 2: Read your DMARC reports for two to four weeks. Get reports flowing in. DMARCeye's free plan covers one domain. Reports show every service sending mail as your domain. For a small business, the list is usually short: your ESP, your hosting provider's mail relay, an invoicing tool, maybe a contact form. Confirm each one is legitimate and check whether it's authenticated.
Step 3: Authenticate the unauthenticated ones. Most ESPs and email tools provide step-by-step DKIM setup. If a service won't authenticate, replace it with one that will.
Step 4: Move from p=none to p=quarantine, then to p=reject. Once your reports are clean for a couple of weeks, tighten the policy. Failed messages first go to spam (p=quarantine), then are refused outright (p=reject).
The whole process takes most small businesses a single afternoon to investigate and a couple of weeks to confirm.
The Practical Takeaway
Small senders are over-represented in the broken tier of DMARC compliance because at small volume, a single misconfiguration moves the percentage a lot. The good news is that small senders also have small footprints. One missing record, one un-aligned tool, one forgotten service. Find it, fix it, and you have a real chance of joining the share of small domains running clean. In our Q1 snapshot, 41.8% of small senders were already at 99% compliance or above.